Government agencies handle a tremendous amount of sensitive information every day, ranging from citizen data and financial records to law enforcement files and healthcare documents. The need to share this data between departments, remote teams, and partner organizations has never been greater. However, doing so without proper safeguards can expose agencies to significant risks, including compliance violations, data breaches, and operational disruptions.
This article provides a comprehensive guide for government agencies on how to share files securely while minimizing compliance risks. By combining technology, policies, and best practices, agencies can maintain data integrity, protect sensitive information, and stay aligned with regulatory requirements.
Introduction
The Importance of Secure File Sharing in Government Operations
Secure file sharing is critical in government operations because agencies routinely exchange highly sensitive information that, if compromised, could affect national security, public trust, or the safety of citizens. Departments often need to collaborate on initiatives such as social services, emergency response, and public health, requiring the seamless and secure government file transfer of documents. By implementing robust file-sharing practices, agencies can improve operational efficiency while safeguarding confidential data.
Risks of Non-Compliant File Sharing
Failing to maintain compliance when sharing files can have serious consequences. Data breaches resulting from unsecured file transfers can lead to financial penalties, legal liabilities, and reputational damage. Non-compliance with regulations such as HIPAA, FISMA, and CJIS can also cause operational delays, as agencies may be required to halt activities or conduct extensive audits after a security incident. Additionally, the mishandling of sensitive information can erode public trust, which is critical for effective governance.
Common Challenges Faced by Government Agencies
Government agencies face unique challenges in file sharing. Many organizations operate across multiple departments and jurisdictions, creating complex workflows. Remote work and distributed teams add another layer of difficulty, as files must be accessed securely outside the agency’s traditional network. Sensitive data, ranging from health records to law enforcement reports, must be protected at all times, requiring a combination of secure technology, strict policies, and staff training.
Overview of Solutions for Secure File Sharing
A successful secure file-sharing strategy combines advanced technology, robust policies, and continuous training. Agencies need tools that encrypt data, control access, and maintain audit logs while integrating with existing IT infrastructure. At the same time, clear policies and procedures must guide employees on proper usage. Together, these measures reduce risks, ensure compliance, and support operational efficiency.
Understanding Compliance Requirements
Key Regulations: HIPAA, FISMA, CJIS, GDPR
Government agencies must adhere to various regulatory frameworks depending on the type of data they handle. HIPAA governs the security of health information, FISMA focuses on federal information systems, and CJIS provides guidelines for criminal justice data. Agencies operating internationally may also need to comply with GDPR when handling EU citizens’ personal information. Each regulation specifies requirements for data protection, access control, and monitoring that must be followed when sharing files.
Penalties and Risks of Non-Compliance
Non-compliance can carry severe consequences. For example, HIPAA violations can result in hefty fines, while failure to meet CJIS standards can prevent access to criminal justice databases. Beyond financial penalties, non-compliance may lead to loss of access to critical systems, operational disruptions, and reputational damage that undermines public trust.
How Compliance Affects IT Infrastructure and Policies
Compliance requirements shape both the technical and procedural aspects of an agency’s file-sharing system. IT infrastructure must support encryption, secure access controls, logging, and monitoring. Policies must outline roles, responsibilities, and acceptable use, ensuring staff understand how to handle sensitive information properly. Compliance is not just about technology—it’s about integrating security into every aspect of the organization.
Role of Audit Trails and Reporting in Compliance
Audit trails and reporting are essential for demonstrating compliance. Every file access, modification, or transfer should be logged in detail to support internal reviews and external audits. Comprehensive logging ensures transparency, helps detect unauthorized activity, and provides evidence of compliance with regulatory mandates.
Department-Specific Compliance Needs
Different departments may have specialized compliance requirements. Health departments prioritize HIPAA, law enforcement agencies focus on CJIS, and finance or procurement teams may need to follow FISMA or other federal standards. Understanding these department-specific requirements allows IT teams to tailor secure file-sharing solutions that meet all applicable regulations.
Risks of Insecure File Sharing
Data Breaches and Cyber Attacks
Insecure file sharing exposes sensitive information to cybercriminals. Unencrypted emails, shared USB drives, and unsecured cloud storage can become entry points for hackers. A single breach can compromise thousands of records, potentially affecting national security, public health, or law enforcement operations.
Insider Threats and Human Error
Not all risks come from external attackers. Employees may inadvertently share files with the wrong person, use unsecured personal devices, or fail to follow policies. Insider threats, whether intentional or accidental, account for a significant portion of government data breaches. Proper training and technology safeguards help minimize these risks.
Loss or Accidental Sharing of Sensitive Information
Without proper controls, files can be accidentally sent to the wrong recipient, uploaded to unsecured locations, or left accessible to unauthorized personnel. These incidents not only violate compliance standards but also compromise sensitive information, potentially resulting in legal and operational consequences.
Consequences on Public Trust and Agency Reputation
Government agencies rely on public trust to function effectively. Any mishandling of sensitive data can erode confidence in the agency’s ability to protect citizen information. Publicized breaches or compliance violations can damage credibility, undermine community relationships, and reduce cooperation with government programs.
Operational Disruption Due to Non-Compliance
Non-compliance can also halt critical operations. Agencies may need to pause data sharing, perform audits, or implement emergency mitigation plans. These disruptions can delay service delivery, affect inter-departmental collaboration, and impact overall mission effectiveness.
Best Practices for Secure File Sharing
Implementing Role-Based Access Control (RBAC)
Role-based access control ensures that employees only have access to the files necessary for their job functions. RBAC limits exposure of sensitive information and reduces the risk of accidental or intentional misuse. By defining roles and permissions clearly, agencies can maintain tight control over file access across departments.
Encryption at Rest and in Transit
Encryption is essential for protecting sensitive files. Encrypting files at rest safeguards data stored on servers, while encrypting in transit protects files moving between systems. Strong encryption protocols ensure that even if files are intercepted, the information remains unreadable to unauthorized parties.
Multi-Factor Authentication (MFA) for Users
MFA adds an extra layer of security by requiring multiple forms of verification before granting access to sensitive files. This significantly reduces the likelihood of unauthorized access, even if login credentials are compromised.
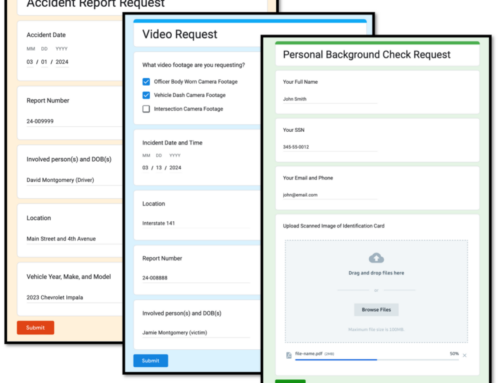
Secure Collaboration Platforms for Inter-Departmental Sharing
Modern secure collaboration platforms allow agencies to share files safely across departments while maintaining compliance controls. These platforms often include encrypted messaging, access restrictions, audit logging, and integration with existing IT systems.
Regular Staff Training and Awareness Programs
Technology alone cannot prevent errors. Staff training ensures employees understand secure file-sharing procedures, recognize potential threats, and follow best practices consistently. Awareness programs can include phishing simulations, policy reviews, and hands-on training sessions.
Automated Audit Trails and Logging
Automated logging of file access and transfer activities provides a comprehensive record for compliance audits. Agencies can monitor who accessed a file, when, and what changes were made, helping to detect anomalies and maintain accountability.
Data Classification and Tagging
Classifying files based on sensitivity ensures that critical data receives higher protection. Tagging files with security levels allows automated systems to apply appropriate encryption, access restrictions, and monitoring measures.
Periodic Security Assessments and Penetration Testing
Regular security assessments help agencies identify vulnerabilities in file-sharing processes. Penetration testing simulates cyber attacks to test defenses, enabling IT teams to remediate weaknesses before they are exploited.
Technology Solutions for Secure File Sharing
Encrypted Cloud Storage Solutions Compliant with Government Standards
Government-compliant cloud solutions provide centralized storage with built-in security features like encryption, access control, and audit logging. These platforms are often certified to meet HIPAA, FISMA, and CJIS standards.
Secure File Transfer Protocols (SFTP, HTTPS, AS2)
Secure transfer protocols protect files during transmission. SFTP, HTTPS, and AS2 ensure data integrity and encryption, minimizing the risk of interception or tampering.
Enterprise Collaboration Tools with Compliance Certifications
Collaboration tools such as Microsoft 365 Government, Google Workspace for Government, or similar platforms offer built-in compliance controls. These solutions allow secure communication, file sharing, and storage across departments.
Virtual Private Networks (VPNs) and Zero-Trust Architectures
VPNs provide secure connections for remote workers, while zero-trust architectures enforce strict verification for every access attempt. Together, these solutions reduce exposure to unauthorized access.
Digital Rights Management (DRM) for Sensitive Documents
DRM allows agencies to control file usage even after sharing. Permissions can restrict printing, copying, or forwarding, ensuring that sensitive documents remain protected at all times.
Integration with Existing Agency IT Systems
Secure file-sharing solutions should integrate seamlessly with existing IT infrastructure, avoiding workflow disruptions and maintaining consistent security policies across all platforms.
Strategies to Avoid Compliance Risks
Establishing Formal Data Sharing Policies and SOPs
Formal policies and standard operating procedures define how files should be shared, accessed, and stored. Clear guidelines help employees understand their responsibilities and reduce the risk of non-compliant behavior.
Regular Audits and Compliance Checks
Routine audits help identify gaps in file-sharing practices and confirm adherence to regulatory standards. Compliance checks prevent small issues from becoming major violations.
Maintaining Proper Documentation for All File-Sharing Activities
Comprehensive records of file-sharing activities, including access logs and transfer records, are essential for demonstrating compliance during audits or investigations.
Using Certified Vendors for File Storage and Transfer
Working with vendors certified to meet government standards reduces risk and ensures that third-party services adhere to compliance requirements.
Incident Response Planning for Data Breaches
Having a clear incident response plan allows agencies to quickly contain and remediate breaches, reducing potential harm and ensuring regulatory reporting requirements are met.
Balancing Security with Operational Efficiency
While strict security measures are necessary, they should not hinder operational workflows. Agencies should implement solutions that maintain security without disrupting productivity.
Frequently Asked Questions (FAQs)
Can cloud storage be used by government agencies without violating compliance?
Yes, if the cloud provider meets applicable regulatory standards and implements proper encryption, access control, and audit logging.
What are the most secure methods to share large files between departments?
Using encrypted file transfer protocols such as SFTP or secure government-certified collaboration platforms is recommended.
How often should agencies audit their file-sharing practices?
Audits should occur at least annually, with additional reviews triggered by significant changes in technology or regulation.
Are encrypted emails enough for sharing sensitive information?
Encrypted emails provide basic security but may lack audit trails and access controls required for compliance. More robust solutions are preferred.
What technologies reduce human error in secure file sharing?
Automated logging, role-based access control, DRM, and secure collaboration platforms minimize the risk of accidental or unauthorized file sharing.
Conclusion
Secure file sharing is essential for government agencies to protect sensitive information and maintain public trust. By combining technology, policies, and staff training, agencies can share files safely while remaining compliant with HIPAA, FISMA, CJIS, and other applicable regulations.
Proactive measures such as encrypted storage, secure transfer protocols, automated audit trails, and formal SOPs reduce the risk of data breaches and operational disruptions. Agencies should focus on solutions that balance security with efficiency, ensuring that workflows remain smooth without compromising compliance.
Ready to strengthen your secure government file transfer process? Contact us today to learn how our reliable, compliant, and secure file-sharing solutions can safeguard your data while streamlining government operations.